Introducing OpenID Connect in ThinLinc Web Access
For the last six months we’ve been working on adding OpenID Connect (OIDC) support to ThinLinc Web Access. And if everything goes according to plan, it will be a part of the upcoming ThinLinc 4.21.0 release.
We have seen a lot of interest in this feature from our customers, and we believe that it has the potential to substantially improve both the security and user experience of ThinLinc Web Access.
In a nutshell, the OIDC protocol allows an application to offload its authentication of users to an OIDC identity provider. This is what you commonly see in plenty of web applications where users can choose to sign in with, for example, their GitHub account or their Google account instead of using their application-specific username and password.
Now, with the introduction of OIDC support in ThinLinc Web Access, we can offer a means of doing SSO in a way that is secure and easy to configure and use. By extension, this will also allow ThinLinc Web Access to be more tightly integrated into our customers infrastructure. Some common use cases are SSO with CAS, Keycloak, Microsoft EntraID, etc.
Note that we haven’t offloaded everything to the identity provider. After users successfully sign in, ThinLinc will still check that they are allowed to access the system.
User Experience
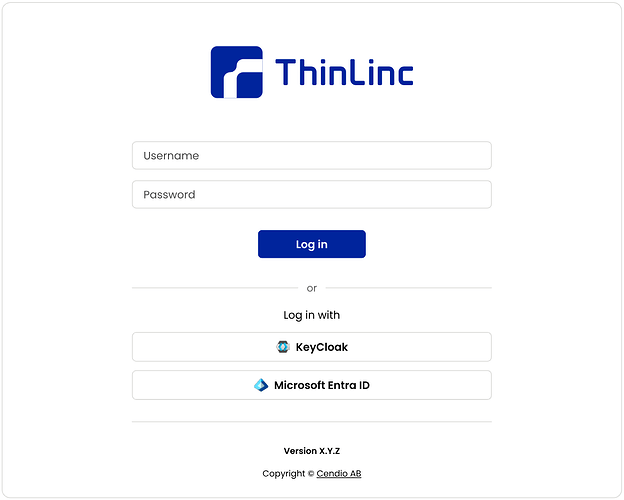
From an end user perspective, we think that logging in with OIDC will feel familiar and effortless. Most users have likely encountered similar login flows when using other popular web applications.
When using OIDC, the login page will show additional buttons that direct users to the system’s configured OIDC identity provider. After signing in, ThinLinc will start their sessions just like they are used to.
Security
For obvious reasons our customers don’t want their users to have to authenticate multiple times, possibly with multiple different sets of credentials just to reach the applications they need. Instead, they want to be able to rely on single sign-on (SSO), such as OIDC, and just have their users authenticate once.
Final thoughts
Working on this project has been a lot of fun, and we are very excited about the final result. I’d say that the largest bulk of time has been dedicated to making sure that we are conforming to the OpenID Connect specification in a manner that is safe in the context of ThinLinc Web Access. It’s important for us to be able to release a feature that we feel is production-ready and that we feel confident in.